GitLab Community Edition on Ubuntu 24.04 on Azure User Guide
Overview
GitLab is the end-to-end DevSecOps platform — Git repository hosting, code review, CI/CD pipelines, container registry, issue tracking, wiki, and security scanning, all in a single self-hosted application. The cloudimg image installs GitLab Community Edition 18 from the official packages.gitlab.com Omnibus package, which bundles PostgreSQL, Redis, Nginx, Puma (Rails app server), Sidekiq (background jobs), Gitaly (Git RPC), and GitLab Workhorse (file uploads + websockets) — no third-party builds. The default root administrator account password is rotated per-VM at first boot.
What is included:
- GitLab Community Edition 18.11.2 from
packages.gitlab.com/gitlab/gitlab-ceOmnibus APT repo - PostgreSQL embedded at
/var/opt/gitlab/postgresql(no separate DB to manage) - Redis embedded at
/var/opt/gitlab/redis - Nginx fronting Puma at
:80(HTTP); GitLab Git SSH on:2222to avoid collision with system sshd - Sidekiq, Gitaly, GitLab Workhorse, GitLab Shell, GitLab KAS, mailroom, alertmanager, prometheus exporters
gitlab-firstboot.servicerotating therootadmin password and rewritingexternal_urlto the VM's IP- Ubuntu 24.04 LTS base with latest security patches
- 24/7 cloudimg support
Prerequisites
Active Azure subscription, SSH key, VNet + subnet. Standard_D4s_v3 (4 vCPU, 16 GB RAM) is the minimum — GitLab Omnibus services together use ~6 GB resident memory under no load. For real teams use Standard_D8s_v3 (8 vCPU, 32 GB) or larger. Allocate at least 50 GB of OS disk; GitLab repository data lives at /var/opt/gitlab/git-data.
Step 1: Deploy from Marketplace
Search "GitLab Community Edition on Ubuntu 24.04 LTS" in Azure Marketplace, click Get It Now → Create. Pick resource group, region, VM size (Standard_D4s_v3 minimum), and SSH key. Allow inbound 22 (SSH), 80 (GitLab HTTP), and 2222 (GitLab Git SSH) in the NSG.
Step 2: SSH into the VM
ssh azureuser@<vm-ip>
The first boot takes 5-8 minutes (GitLab gitlab-ctl reconfigure re-renders nginx + restarts services after the per-VM external_url is set). Wait for /var/lib/cloudimg/gitlab-firstboot.done to appear before browsing.
while [ ! -f /var/lib/cloudimg/gitlab-firstboot.done ]; do echo "waiting..."; sleep 15; done; echo "READY"
Step 3: Verify Services
sudo gitlab-ctl status
Every line should start run: (services up). If you see down: for any service, give it another 60s — Puma and Workhorse can take a moment after reconfigure.
Step 4: Read the Per-VM root Password
sudo cat /stage/scripts/gitlab-credentials.log
Pick up GITLAB_ROOT_PASSWORD and GITLAB_LOGIN_URL. Treat these as secrets — the file is mode 0600 root:root.
Step 5: Configure your Public URL (Important)
Azure VMs with Standard public IPs do not return the public IP via Azure IMDS, so the build script sets external_url to the VM's private IP. Before exposing GitLab to real users, edit external_url to your actual hostname or public IP and re-run reconfigure:
sudo sed -i "s|^external_url .*|external_url 'http://your-gitlab.example.com'|" /etc/gitlab/gitlab.rb
sudo gitlab-ctl reconfigure
If you have HTTPS available (Let's Encrypt), use https:// and GitLab will auto-renew once you set letsencrypt['enable'] = true in the same file.
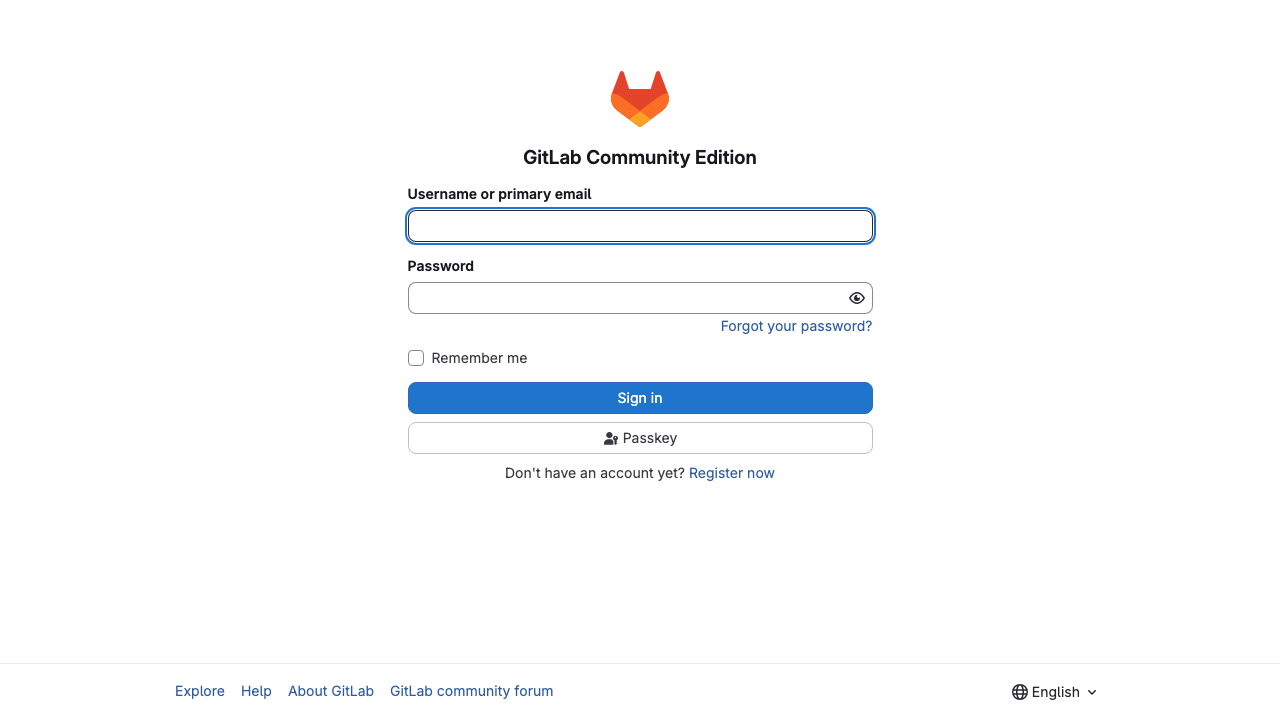
Step 6: Sign In
Browse to http://<vm-ip>/users/sign_in and authenticate as root with the password from Step 4.
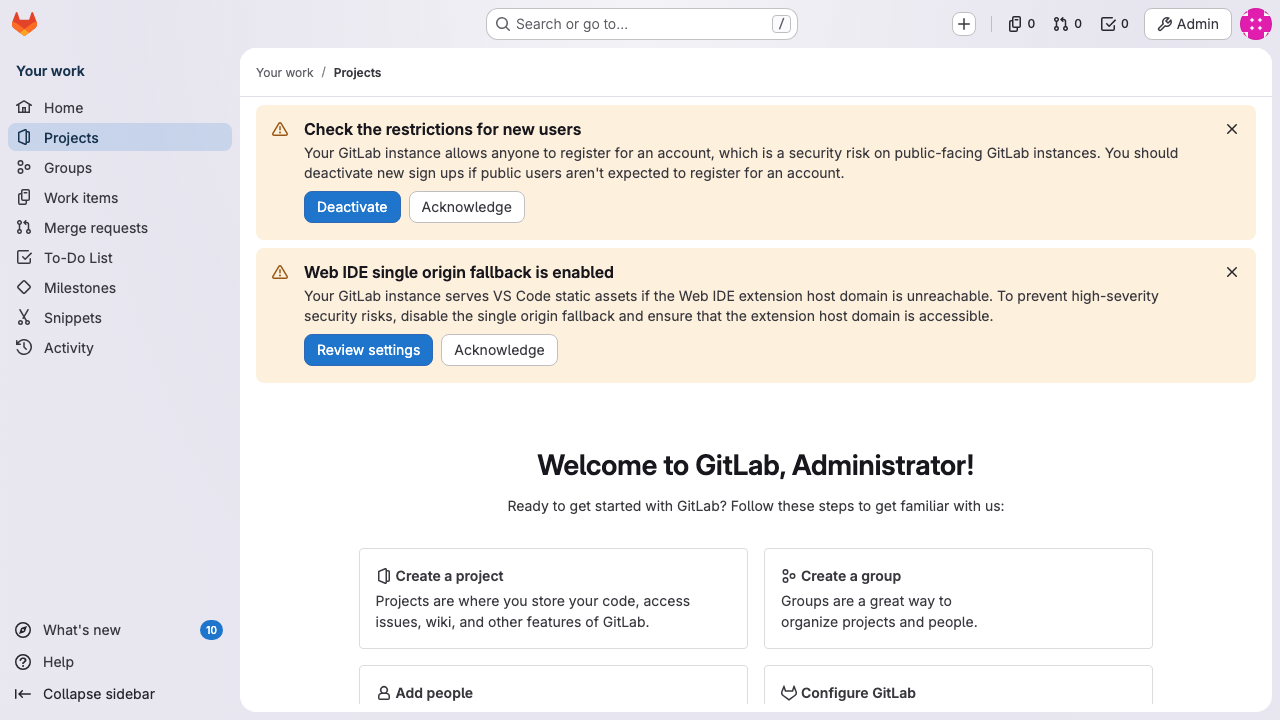
Step 7: Welcome / Projects
After sign-in you land on the welcome view. Create your first project to get a Git remote URL.
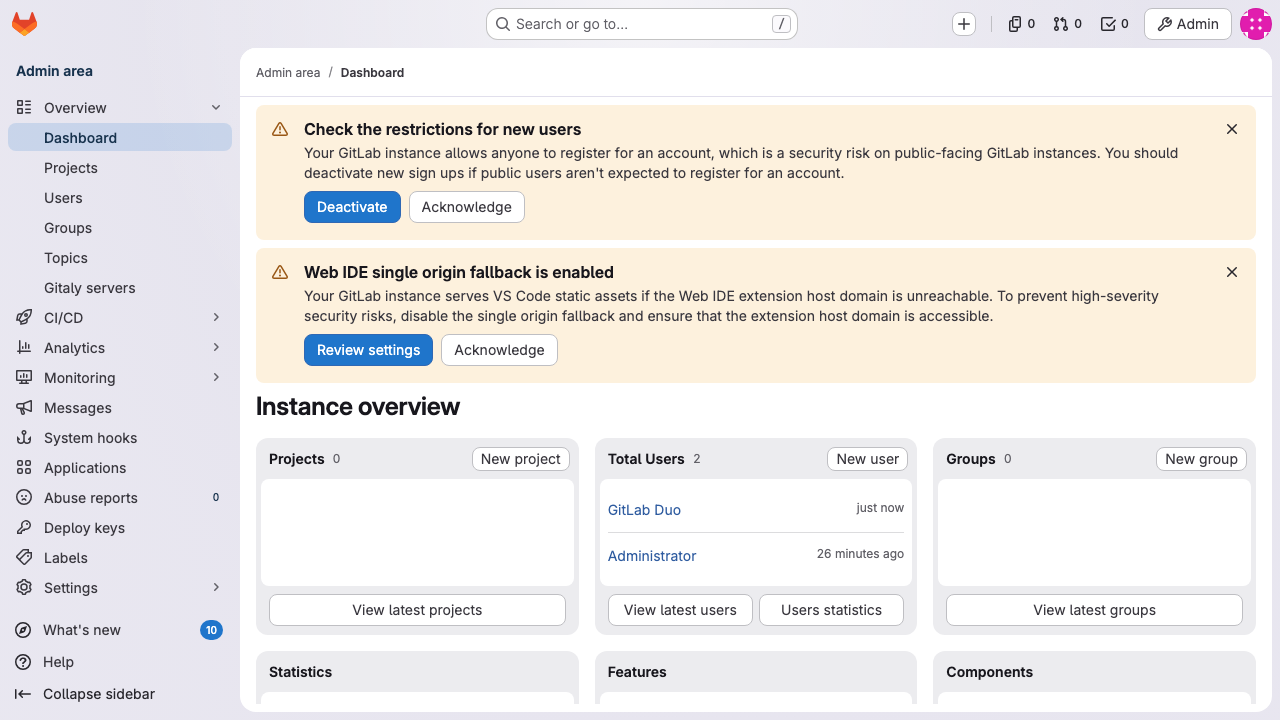
Step 8: Admin Area
Visit /admin for the administration overview — users, groups, runners, jobs, settings, monitoring.
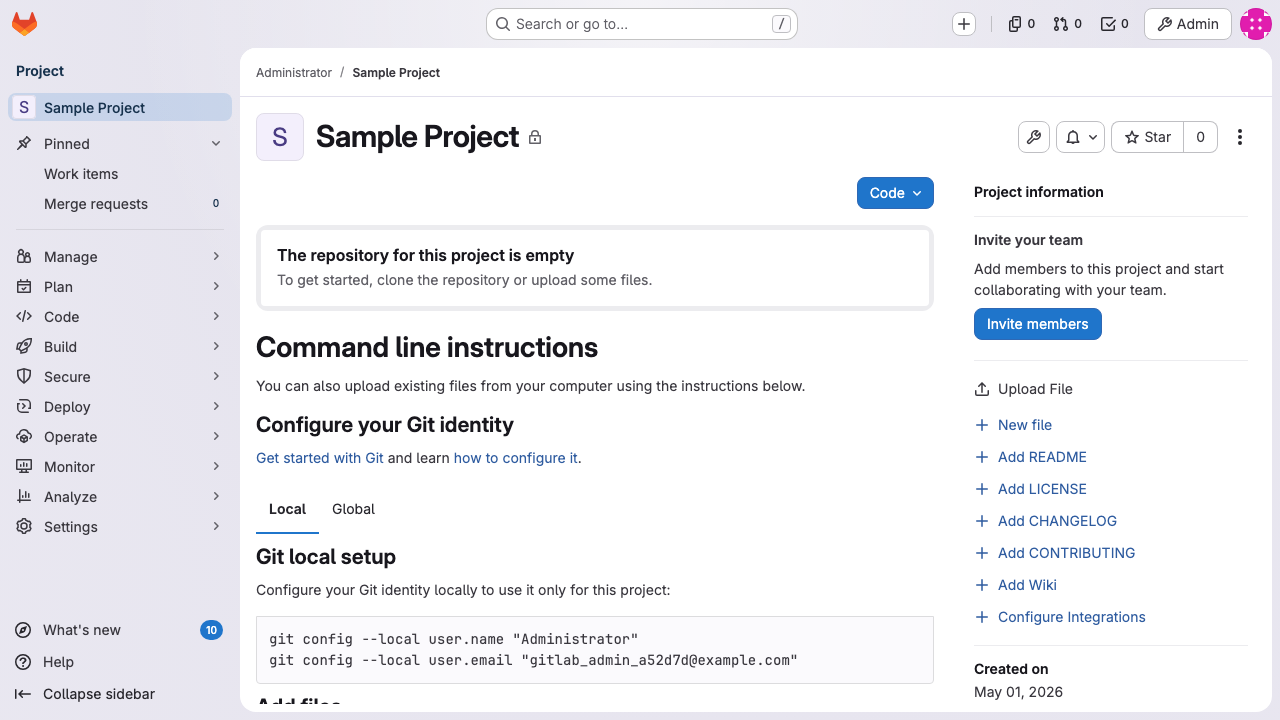
Step 9: Git Push over SSH
GitLab Git SSH listens on port 2222 (system sshd is on 22). Add the port to your remote URL or ~/.ssh/config:
git remote set-url origin ssh://git@<vm-ip>:2222/root/sample-project.git
git push origin main
Step 10: Components
| Component | Path |
|---|---|
| GitLab install root | /opt/gitlab/ |
| GitLab data | /var/opt/gitlab/ |
| GitLab config | /etc/gitlab/gitlab.rb |
| Repositories | /var/opt/gitlab/git-data/repositories/ |
| Embedded PostgreSQL | /var/opt/gitlab/postgresql/ |
| Embedded Redis | /var/opt/gitlab/redis/ |
| GitLab logs | /var/log/gitlab/<service>/current |
| Reconfigure logs | /var/log/gitlab/reconfigure/*.log |
| Firstboot script | /usr/local/sbin/gitlab-firstboot.sh |
| Credentials | /stage/scripts/gitlab-credentials.log (mode 0600 root:root) |
Step 11: Backup
GitLab's official backup tool dumps repos + DB + uploads + container registry into a single tarball:
sudo gitlab-backup create
ls -la /var/opt/gitlab/backups/
Store the resulting .tar somewhere off-VM (Azure Blob, S3). Restore with gitlab-backup restore BACKUP=<timestamp>.
Step 12: Security
- HTTPS: edit
external_url 'https://...'in/etc/gitlab/gitlab.rb, setletsencrypt['enable'] = true, thensudo gitlab-ctl reconfigure. GitLab will obtain and auto-renew a Let's Encrypt cert. - Restrict NSG to your management CIDR for ports 22 + 2222; restrict 80/443 to your CDN or office IPs only.
- Enforce 2FA under Admin → Settings → Sign-up restrictions, or per-user under
/profile/two_factor_auth. - Sign in with SSO — GitLab supports OIDC, SAML, LDAP, Azure AD, Microsoft Entra ID. Configure in
/etc/gitlab/gitlab.rbthen reconfigure. - Patch monthly:
sudo apt-get update && sudo apt-get upgrade && sudo gitlab-ctl restart. GitLab CE releases patch versions monthly + a major every quarter. - Backup before upgrades:
sudo gitlab-backup createthensudo apt-get install gitlab-ce.
Licensing
GitLab Community Edition is MIT licensed — free to use commercially. cloudimg provides commercial support separately. support@cloudimg.co.uk.