Red Hat JBoss EAP 8.1 on Red Hat Enterprise Linux 8 on Azure User Guide
Overview
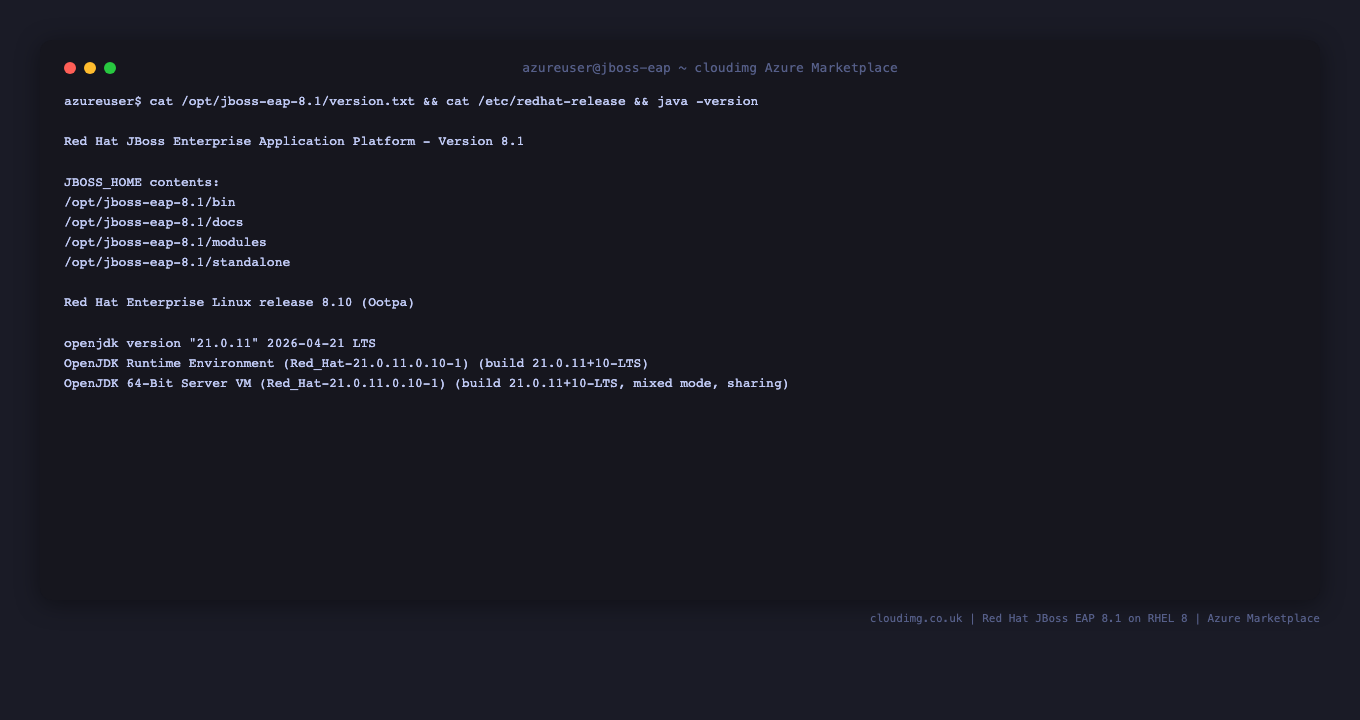
This guide covers the deployment and configuration of Red Hat JBoss EAP 8.1 (the productized release of WildFly running on Jakarta EE 10) on Red Hat Enterprise Linux 8 on Microsoft Azure using cloudimg's pre configured virtual machine image. JBoss EAP 8.1 supports the Jakarta EE 10 Web and Full profiles plus MicroProfile, ships with Undertow as the HTTP engine, and exposes a web based management console plus a CLI for deployment and runtime administration. cloudimg ships EAP pre installed under /opt/jboss-eap-8.1, with a system managed jboss-eap.service running the standalone-full.xml profile, and a firstboot service that rotates the management admin password to a per VM unique value on first customer boot.
What's included in this VM image:
- Red Hat JBoss EAP 8.1.0 extracted to
/opt/jboss-eap-8.1, owned by thejbosssystem user - OpenJDK 21 LTS (
java-21-openjdkfrom the RHEL 8 AppStream) — EAP 8.1 supports JDK 17 LTS and JDK 21 LTS, we ship 21 jboss-eap.servicesystemd unit running thestandalone-full.xmlprofile, bound on0.0.0.0for both HTTP (8080) and Management (9990)jboss-eap-firstboot.servicerotates the ManagementRealmadminpassword per VM on first customer boot- firewalld rules for TCP 8080 and 9990 already opened on the OS
- Latest RHEL 8 security patches applied at build time
Platform: Microsoft Azure (Gen2 Hyper V)
Default OS user: azureuser
EAP runtime user: jboss (no shell)
Step 1: Deploy the Virtual Machine
az vm create -g <resource-group> -n jboss-eap-vm -l eastus \
--image cloudimg:jboss-eap-8-1-rhel-8:basic:latest \
--size Standard_B2s \
--admin-username azureuser \
--ssh-key-values ~/.ssh/id_rsa.pub
Standard_B2s (4 GB RAM) is enough for the default standalone-full profile under light load. For production traffic, choose Standard_E4s_v5 (4 vCPU, 32 GB RAM) and tune the JVM heap as in Step 9.
Step 2: Connect via SSH
ssh azureuser@<public-ip>
Confirm the OS:
cat /etc/redhat-release
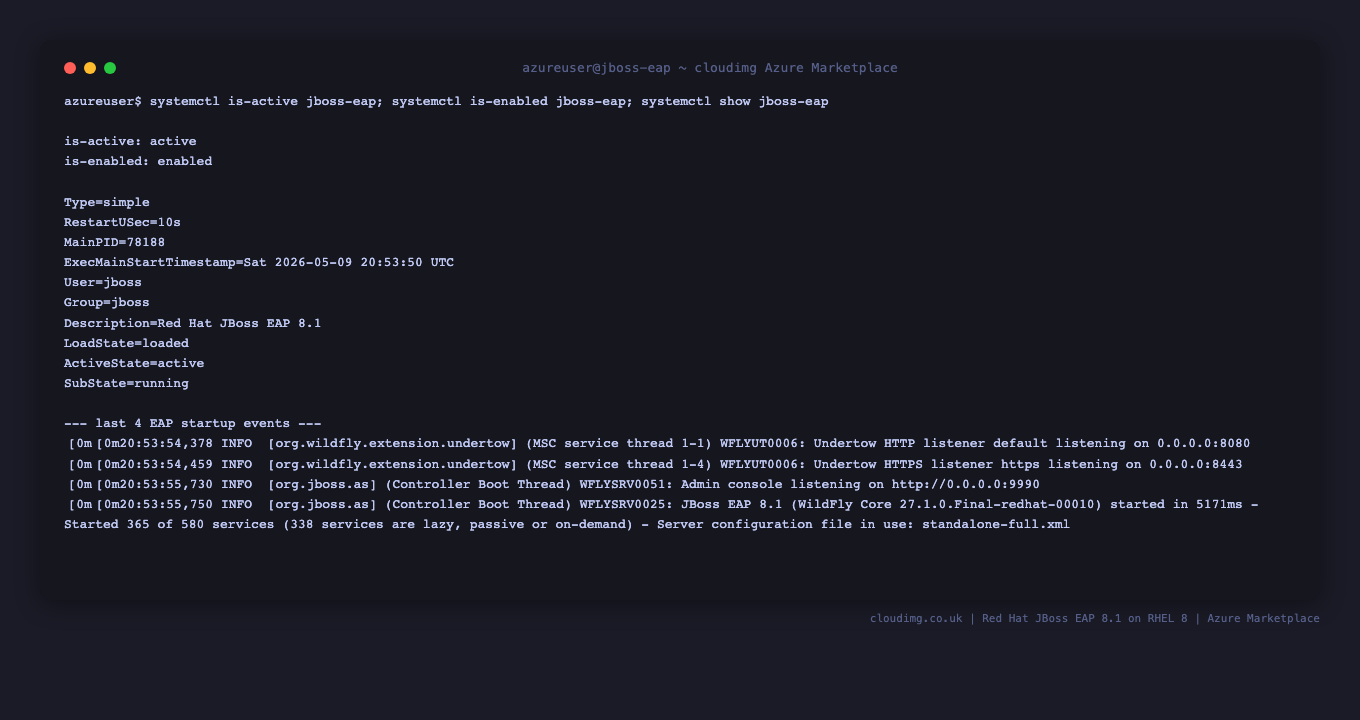
Step 3: Confirm the EAP Server is Running
jboss-eap.service starts automatically at boot.
sudo systemctl is-active jboss-eap.service
sudo systemctl is-enabled jboss-eap.service
Inspect the unit:
sudo systemctl show jboss-eap.service -p Description -p ActiveState -p SubState -p MainPID -p User
Step 4: Locate the Per VM Admin Password
The jboss-eap-firstboot.service rotates the management admin password on first boot and writes the new credentials to /home/azureuser/CREDENTIALS.txt.
sudo cat /home/azureuser/CREDENTIALS.txt
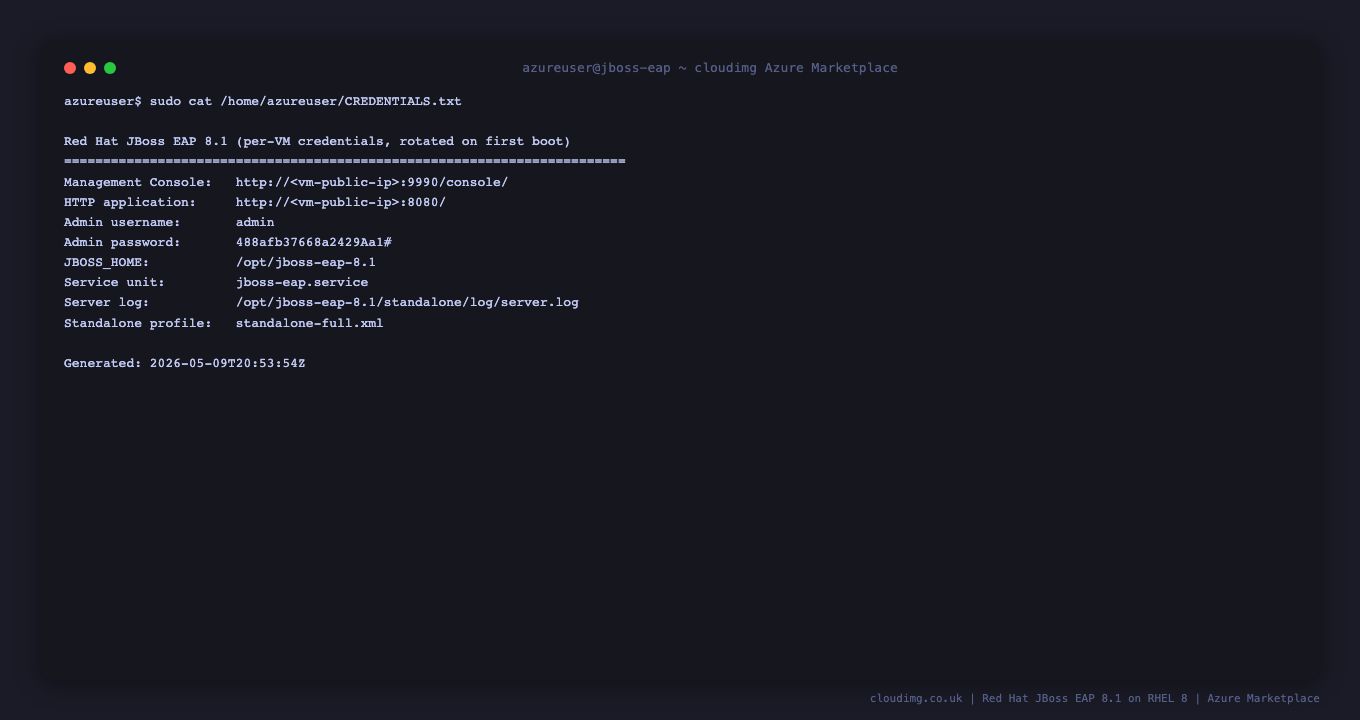
Copy the password to a secure location. The file is owned by root:root with mode 0600. Remove it once you have the password stored elsewhere.
Step 5: Confirm EAP is Listening on 8080 and 9990
sudo ss -tlnp | grep -E ':8080|:9990'

You should see entries showing 0.0.0.0:8080 (HTTP for deployed applications) and 0.0.0.0:9990 (the management console + management API), both owned by the java process running EAP.
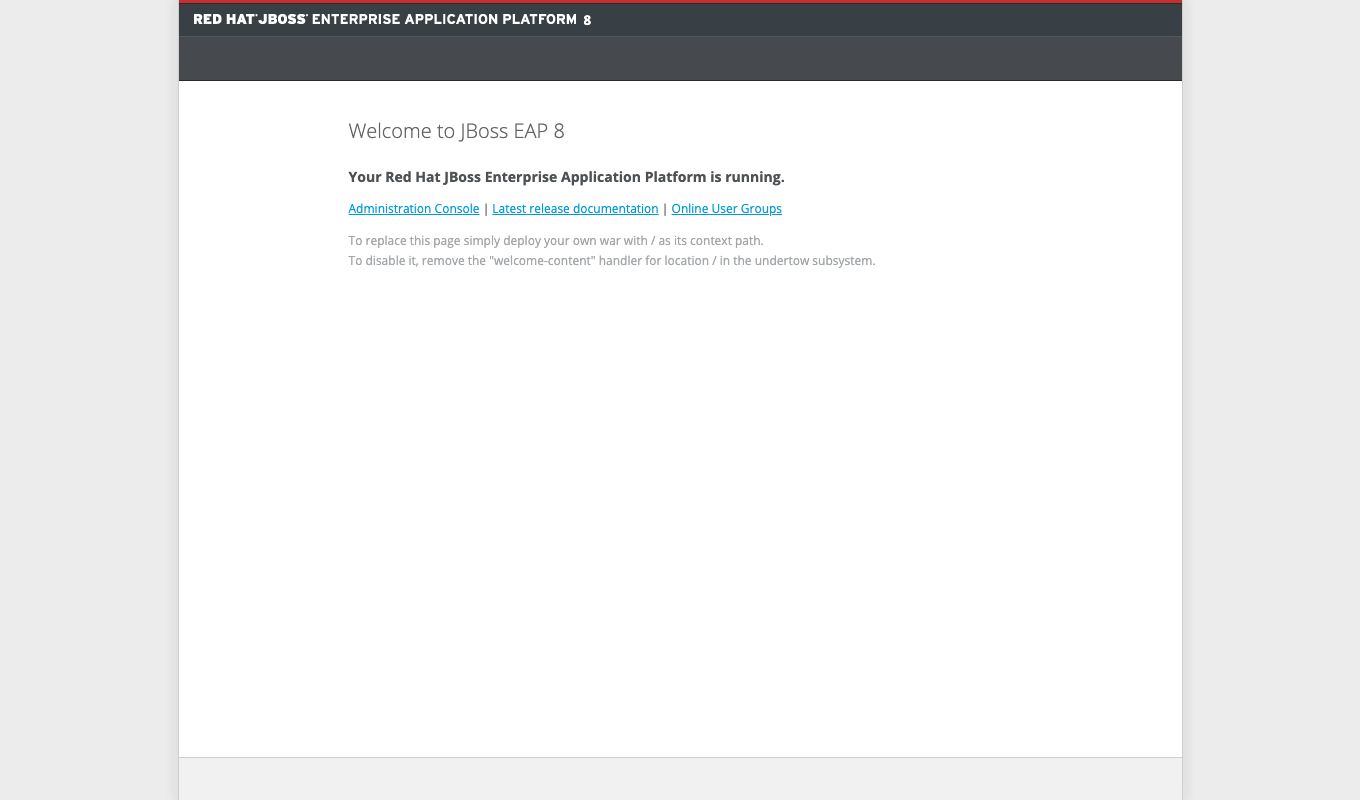
Open a browser to the EAP welcome page on port 8080 to confirm the application server is reachable from outside the VM (this is the default landing for any HTTP request that does not match a deployed application context):
Step 6: Connect to the Management Console
Open a browser to the public IP on port 9990 — the management console is served over HTTP on the standalone-full profile by default:
echo "http://<vm-public-ip>:9990/console/"
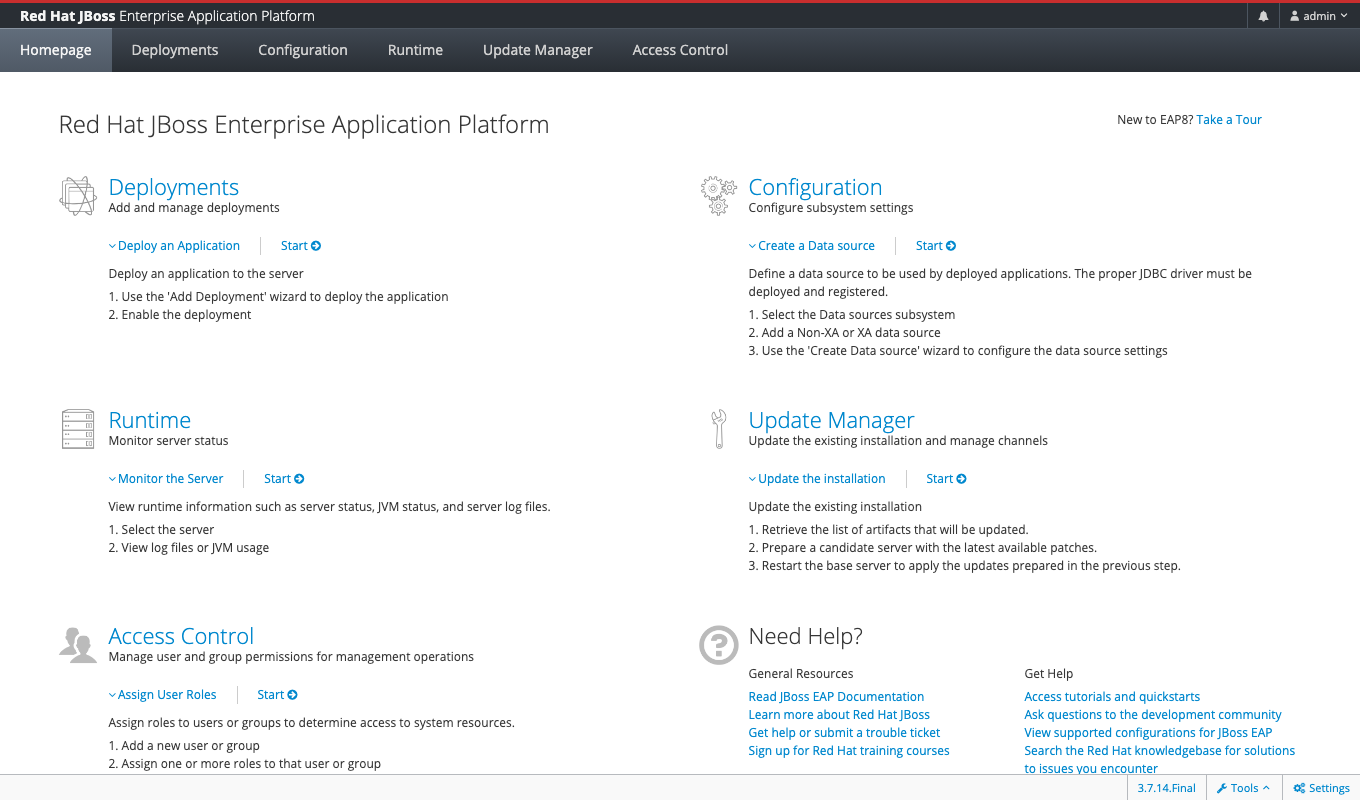
Sign in with the username admin and the per VM password from Step 4. EAP uses HTTP digest authentication, so most browsers will pop a native login dialog the first time you hit the URL. The console then drops you onto the Homepage view.
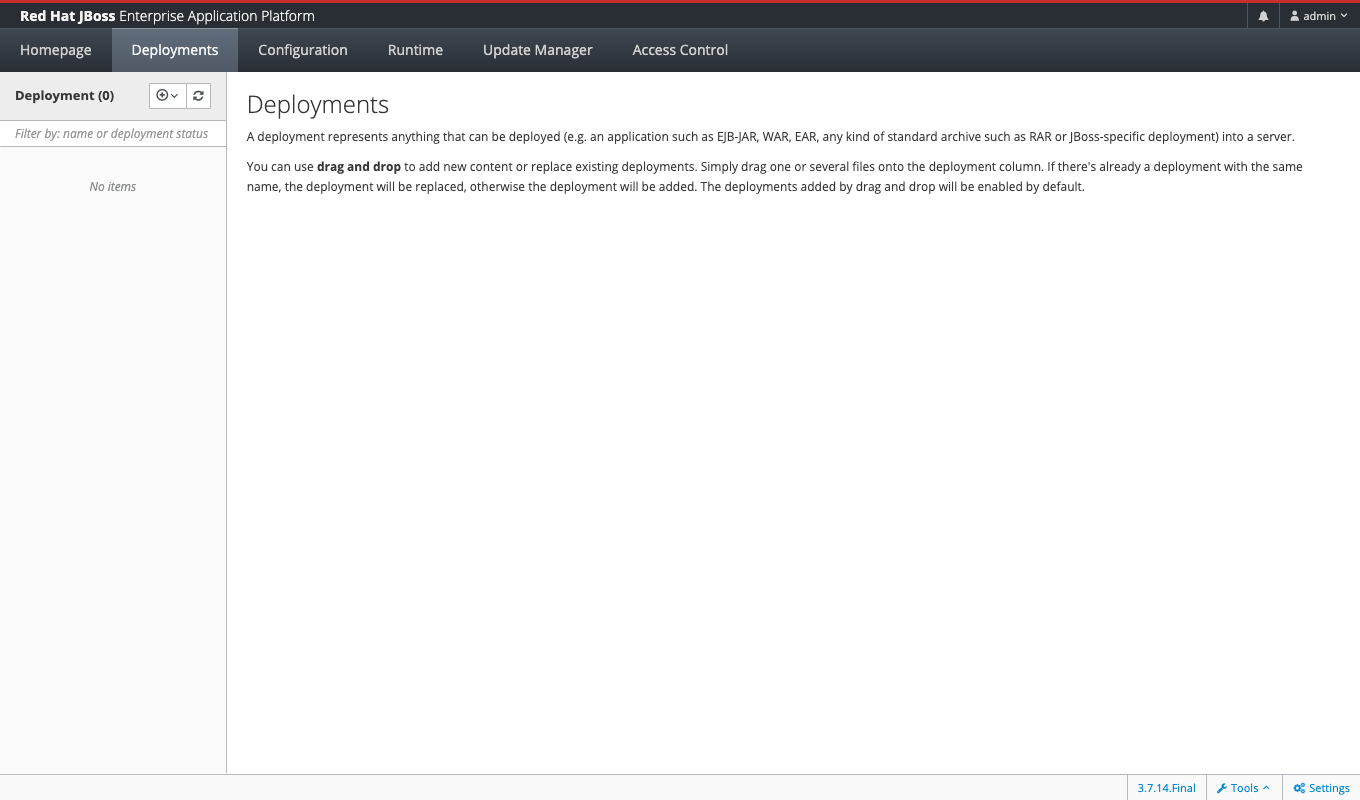
The Deployments tab shows applications currently deployed to the server. A fresh image starts empty — drag-and-drop a WAR file into the deployment column or use the CLI in Step 8.
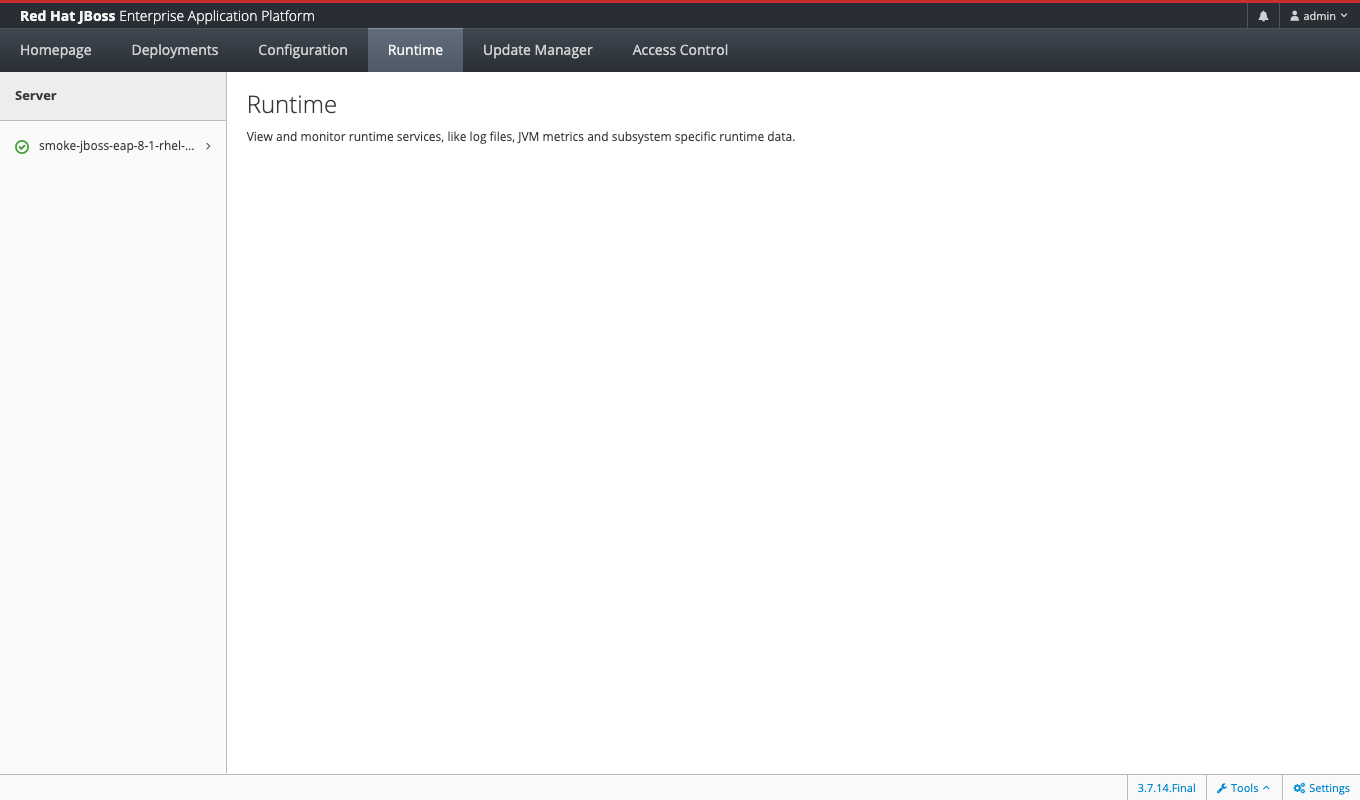
The Runtime tab is where you monitor the live server: log files, JVM metrics, datasource pools, web subsystem statistics. The cloudimg image registers the VM hostname as the only server entry, with a green health indicator.
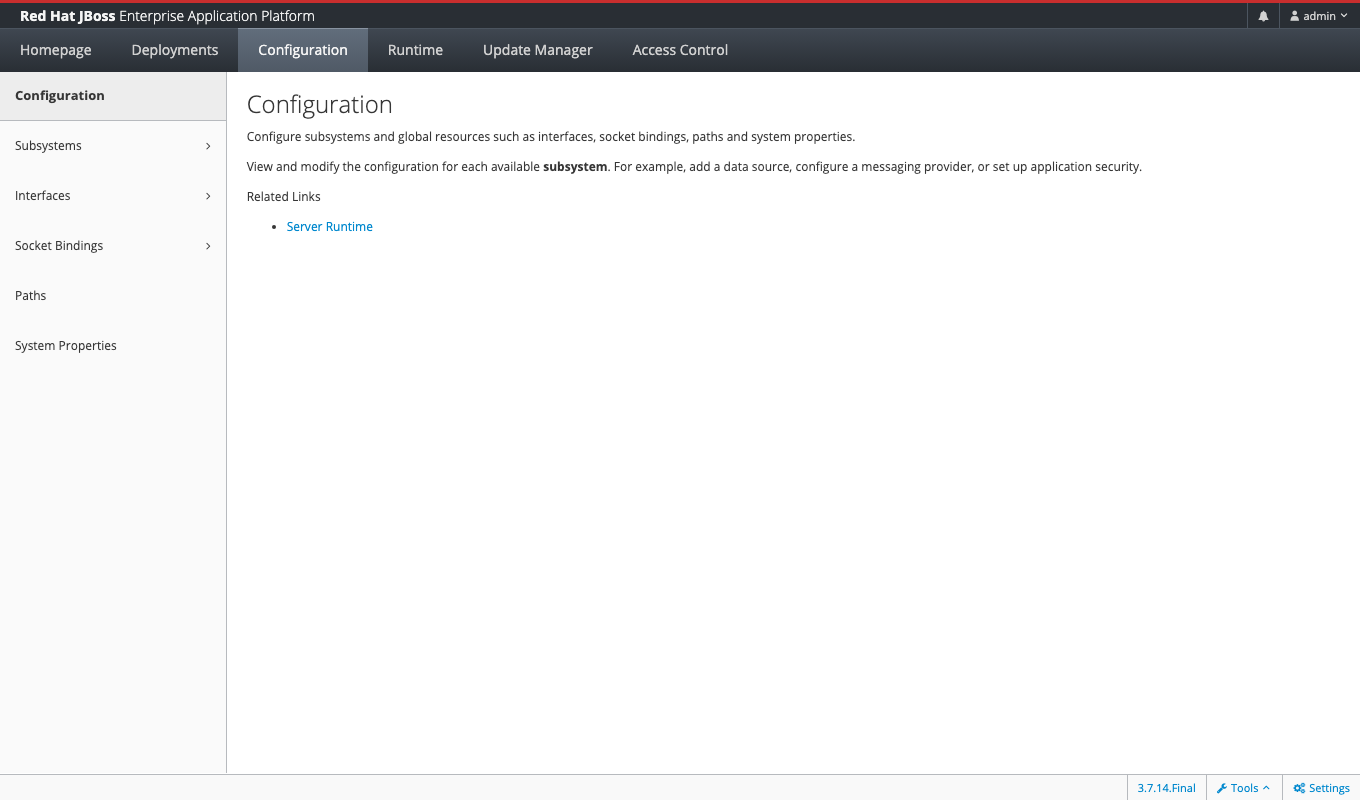
The Configuration tab gives you the full subsystem tree — datasources, messaging-activemq, transactions, undertow, infinispan, and so on. This is the GUI equivalent of the JBoss CLI and lets you make most administrative changes without dropping to the command line.
For a production install you should restrict the management interface to a private VNet subnet (Step 7) and switch the management console to HTTPS (Step 11).
Step 7: Open the Azure NSG for HTTP and Management
The OS firewalld already permits 8080 and 9990, but the Azure Network Security Group attached to the VM blocks them by default. Open them only from the subnets that need access — never from 0.0.0.0/0 for production:
az network nsg rule create -g <resource-group> --nsg-name <nsg-name> \
-n allow-eap-http \
--priority 200 --direction Inbound --access Allow \
--protocol Tcp --source-address-prefixes 10.0.0.0/16 \
--destination-port-ranges 8080
az network nsg rule create -g <resource-group> --nsg-name <nsg-name> \
-n allow-eap-mgmt \
--priority 210 --direction Inbound --access Allow \
--protocol Tcp --source-address-prefixes 10.0.0.0/16 \
--destination-port-ranges 9990
Replace 10.0.0.0/16 with your application subnet's CIDR for HTTP, and tighten the management rule to your operations subnet only.
Step 8: Deploy a WAR File via the Management CLI
Copy a WAR to the VM and deploy it via the JBoss CLI. The CLI authenticates against the same ManagementRealm credentials as the console (substitute the path to your own WAR):
sudo -u jboss /opt/jboss-eap-8.1/bin/jboss-cli.sh \
--connect \
--user=admin --password="$(grep '^Admin password:' /home/azureuser/CREDENTIALS.txt | awk '{print $3}')" \
--command="deploy /home/azureuser/myapp.war"
List active deployments (read only, safe to run as is):
sudo -u jboss /opt/jboss-eap-8.1/bin/jboss-cli.sh \
--connect \
--user=admin --password="$(grep '^Admin password:' /home/azureuser/CREDENTIALS.txt | awk '{print $3}')" \
--command="deployment-info"
Undeploy:
sudo -u jboss /opt/jboss-eap-8.1/bin/jboss-cli.sh \
--connect \
--user=admin --password="$(grep '^Admin password:' /home/azureuser/CREDENTIALS.txt | awk '{print $3}')" \
--command="undeploy myapp.war"
Step 9: Tune the JVM Heap for Larger VMs
cloudimg uses EAP's default Xms1303m -Xmx1303m (about 1.3 GB heap) which fits the Standard_B2s build target (4 GB RAM total). On a larger SKU, raise both values to roughly 50 to 70 percent of system RAM. Edit the systemd drop in (replace <your-min-heap> and <your-max-heap> with values appropriate for your VM size, e.g. 8g and 8g on a Standard_E4s_v5 with 32 GB):
sudo mkdir -p /etc/systemd/system/jboss-eap.service.d
sudo tee /etc/systemd/system/jboss-eap.service.d/heap.conf >/dev/null <<'CONF'
[Service]
Environment=JAVA_OPTS=-Xms<your-min-heap> -Xmx<your-max-heap> -Djava.net.preferIPv4Stack=true -Djboss.modules.system.pkgs=org.jboss.byteman -Djava.awt.headless=true
CONF
sudo systemctl daemon-reload
sudo systemctl restart jboss-eap.service
Verify the JVM picked up the new value:
sudo journalctl -u jboss-eap.service --no-pager -n 20 | grep -E 'Xms|Xmx'
Step 10: Configure Datasources
EAP 8.1 ships ExampleDS (an embedded H2) by default. Add a production datasource — for example PostgreSQL — by copying the JDBC driver into the modules tree and registering a datasource via the CLI (substitute your own database connection details):
sudo -u jboss /opt/jboss-eap-8.1/bin/jboss-cli.sh \
--connect \
--user=admin --password="$(grep '^Admin password:' /home/azureuser/CREDENTIALS.txt | awk '{print $3}')" \
--command="data-source add --name=AppDS --jndi-name=java:jboss/datasources/AppDS --driver-name=postgresql --connection-url=jdbc:postgresql://<your-db-host>:5432/<your-db-name> --user-name=<your-db-user> --password=<your-db-password> --use-ccm=true --enabled=true"
Test the connection:
sudo -u jboss /opt/jboss-eap-8.1/bin/jboss-cli.sh \
--connect \
--user=admin --password="$(grep '^Admin password:' /home/azureuser/CREDENTIALS.txt | awk '{print $3}')" \
--command="/subsystem=datasources/data-source=AppDS:test-connection-in-pool"
Step 11: SSL/TLS for the Management Console
For production you should serve the management console over HTTPS. Add a key-store via the CLI (replace changeit with a real keystore password from Azure Key Vault):
sudo -u jboss /opt/jboss-eap-8.1/bin/jboss-cli.sh \
--connect \
--user=admin --password="$(grep '^Admin password:' /home/azureuser/CREDENTIALS.txt | awk '{print $3}')" \
--command="/subsystem=elytron/key-store=mgmtKS:add(path=mgmt.keystore,relative-to=jboss.server.config.dir,credential-reference={clear-text=changeit},type=PKCS12)"
Then create a key-manager and server-ssl-context, attach the HTTPS listener to port 9993 and switch the management console to it. The exact CLI sequence is in the Red Hat JBoss EAP 8.1 documentation — Configuring SSL for the Management Console.
Managing the Server
Restart EAP (waits for the management port to come back up):
sudo systemctl restart jboss-eap.service
for i in $(seq 1 60); do ss -tln 2>/dev/null | grep -q ':9990 ' && break; sleep 2; done
sudo systemctl is-active jboss-eap.service
Tail the server log:
sudo tail -30 /opt/jboss-eap-8.1/standalone/log/server.log
Trigger a graceful shutdown via CLI (preferred for in flight requests over systemctl stop):
sudo -u jboss /opt/jboss-eap-8.1/bin/jboss-cli.sh \
--connect \
--user=admin --password="$(grep '^Admin password:' /home/azureuser/CREDENTIALS.txt | awk '{print $3}')" \
--command=":shutdown"
Switching to a Different Profile
The image runs standalone-full.xml which includes the messaging, EJB, and JCA subsystems. To switch to the lighter standalone.xml (web profile only), edit the systemd drop in:
sudo sed -i 's/standalone-full.xml/standalone.xml/' /etc/systemd/system/jboss-eap.service
sudo systemctl daemon-reload
sudo systemctl restart jboss-eap.service
The other profiles bundled with EAP 8.1: standalone-ha.xml (web profile + clustering), standalone-full-ha.xml (full profile + clustering).
Common Errors
"Authentication failed for user 'admin'" — firstboot has rotated the password. Re read /home/azureuser/CREDENTIALS.txt.
"Connection refused (Connection refused)" on port 9990 — EAP is bound to 0.0.0.0 but the Azure NSG is blocking. See Step 7.
"Address already in use: bind" in the server log — something else on the VM is using 8080 or 9990. Use sudo ss -tlnp | grep -E ':8080|:9990' to find the conflicting process.
"OutOfMemoryError: Java heap space" — bump -Xmx per Step 9 or move to a larger VM SKU.
"java.security.cert.CertificateException" when connecting to a TLS endpoint from inside EAP — the JDK truststore at /usr/lib/jvm/jre-21-openjdk/lib/security/cacerts does not include your private CA. Add it with sudo keytool -import -trustcacerts -file <ca>.crt -keystore /usr/lib/jvm/jre-21-openjdk/lib/security/cacerts -alias <name>.
On Startup
jboss-eap.service is enabled at boot via systemd:
sudo systemctl is-enabled jboss-eap.service
jboss-eap-firstboot.service runs once on the very first customer boot to rotate the admin password, then stays in active (exited) and is a no op on subsequent reboots.
Support
cloudimg provides 24/7 expert support for this image. Contact support@cloudimg.co.uk.
Licensing note: Red Hat JBoss EAP is a Red Hat product subject to the Red Hat End User License Agreement. cloudimg packages the developer build for evaluation and development use; production deployments require a Red Hat subscription. Contact your Red Hat account team for production licensing or use Red Hat's no cost developer subscription via developers.redhat.com. cloudimg charges a per vCPU per hour fee for packaging, security patching, and 24/7 operational support — this is separate from any Red Hat subscription you hold.