MariaDB 10.11 LTS on Ubuntu 24.04 on Azure User Guide
Overview
This guide covers the deployment and configuration of MariaDB 10.11 LTS on Ubuntu 24.04 on Azure using cloudimg Azure Marketplace images. MariaDB is the community-developed, drop-in-compatible fork of MySQL maintained by the MariaDB Foundation.
MariaDB 10.11 is the final 10.x long-term-support release, supported through February 2028. It is the right choice for production workloads with stacks pinned to the 10.x branch — older application schemas, ORM compatibility constraints, Galera 10.x clusters, MaxScale 10.x deployments, and Percona toolkit pinned to 10.x. For greenfield deployments without a 10.x dependency, consider the cloudimg MariaDB 11 LTS image instead — that line ships the newer engine and receives patches into 2029.
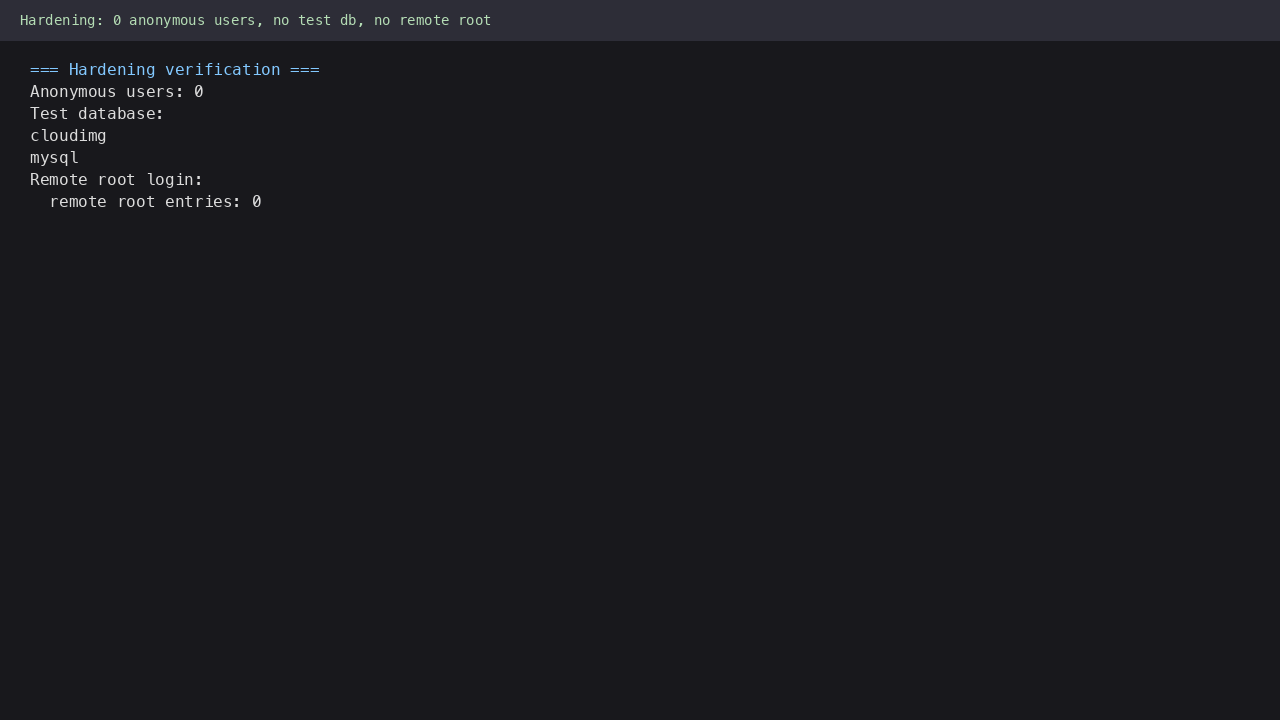
The image ships MariaDB 10.11 from the official MariaDB Foundation APT repository at mariadb.org pinned to noble (Ubuntu 24.04). On every fresh customer virtual machine, mariadb-firstboot.service rotates the root password from the build-time temp value to a per-VM strong password, applies hardening (anonymous users dropped, test database dropped, remote root login disabled), creates the default cloudimg database with utf8mb4 character set, and provisions a cloudimg user with all privileges on it. Credentials are written to /stage/scripts/mariadb-credentials.log (mode 0600). No two virtual machines ever share a password; no password is baked into the image.
What is included:
-
MariaDB 10.11 LTS server from the official MariaDB Foundation APT repository
-
Listener on TCP 3306 bound to 127.0.0.1 by default (Ubuntu noble packaging default; see Step 9 to allow remote connections)
-
mariadb,mariadb-admin,mariadb-dumpclients (with legacymysql-prefixed symlinks) -
Per-VM root password generated on first boot, written to
/stage/scripts/mariadb-credentials.log -
Default
cloudimgdatabase (utf8mb4, utf8mb4_unicode_ci collation) -
cloudimguser with all privileges on thecloudimgdatabase -
Hardening applied at firstboot: anonymous users dropped,
testdatabase dropped, remote root login disabled -
Systemd service
mariadb.servicefor automatic startup -
Idempotent firstboot service
mariadb-firstboot.service -
Ubuntu 24.04 LTS base with latest security patches applied at build time
-
Azure Linux Agent for seamless cloud integration and SSH key injection
-
24/7 cloudimg support with guaranteed 24 hour response SLA
Prerequisites
-
An active Azure subscription
-
A subscription to the MariaDB 10.11 LTS on Ubuntu 24.04 listing on Azure Marketplace
-
An SSH public key for VM authentication
-
A virtual network and subnet in the target region
Recommended virtual machine size: Standard_D2s_v3 (2 vCPU, 8 GB RAM) for production. MariaDB benefits from RAM for the InnoDB buffer pool. Standard_B2s is sufficient for development.
Step 1: Deploy from the Azure Portal
Navigate to Marketplace in the Azure Portal, search for MariaDB 10.11 LTS, and select the cloudimg publisher entry. Click Create.
On the Networking tab attach a network security group that allows inbound TCP 22 from your management IP range and TCP 3306 only from application server subnets or the virtual network CIDR. Do not expose port 3306 to the public internet. The root password is written in plain text on the VM by design so you can read it without a second trip; an internet-exposed MariaDB port would make brute-force attacks trivial.
Click Review + create, wait for validation, then Create. Deployment takes around two minutes.
Step 2: Deploy from the Azure CLI
RG="mariadb-prod"
LOCATION="eastus"
VM_NAME="mariadb-01"
ADMIN_USER="azureuser"
GALLERY_IMAGE_ID="/subscriptions/<sub-id>/resourceGroups/azure-cloudimg/providers/Microsoft.Compute/galleries/cloudimgGallery/images/mariadb-10-11-lts-ubuntu-24-04/versions/<version>"
SSH_KEY="$(cat ~/.ssh/id_rsa.pub)"
az group create --name "$RG" --location "$LOCATION"
az network vnet create \
--resource-group "$RG" \
--name mariadb-vnet --address-prefix 10.92.0.0/16 \
--subnet-name mariadb-subnet --subnet-prefix 10.92.1.0/24
az network nsg create --resource-group "$RG" --name mariadb-nsg
az network nsg rule create \
--resource-group "$RG" --nsg-name mariadb-nsg \
--name allow-ssh --priority 100 \
--source-address-prefixes "<your-mgmt-cidr>" \
--destination-port-ranges 22 --access Allow --protocol Tcp
az network nsg rule create \
--resource-group "$RG" --nsg-name mariadb-nsg \
--name allow-mariadb-vnet --priority 110 \
--source-address-prefixes 10.92.0.0/16 \
--destination-port-ranges 3306 --access Allow --protocol Tcp
az vm create \
--resource-group "$RG" --name "$VM_NAME" \
--image "$GALLERY_IMAGE_ID" \
--size Standard_D2s_v3 --storage-sku StandardSSD_LRS \
--admin-username "$ADMIN_USER" --ssh-key-values "$SSH_KEY" \
--vnet-name mariadb-vnet --subnet mariadb-subnet --nsg mariadb-nsg \
--public-ip-address ""
The --public-ip-address "" flag keeps the database off the public internet.
Step 3: Connect via SSH
ssh azureuser@<private-ip>
mariadb.service will already be running and mariadb-firstboot.service will already have run, generating per-VM credentials and creating the cloudimg database.
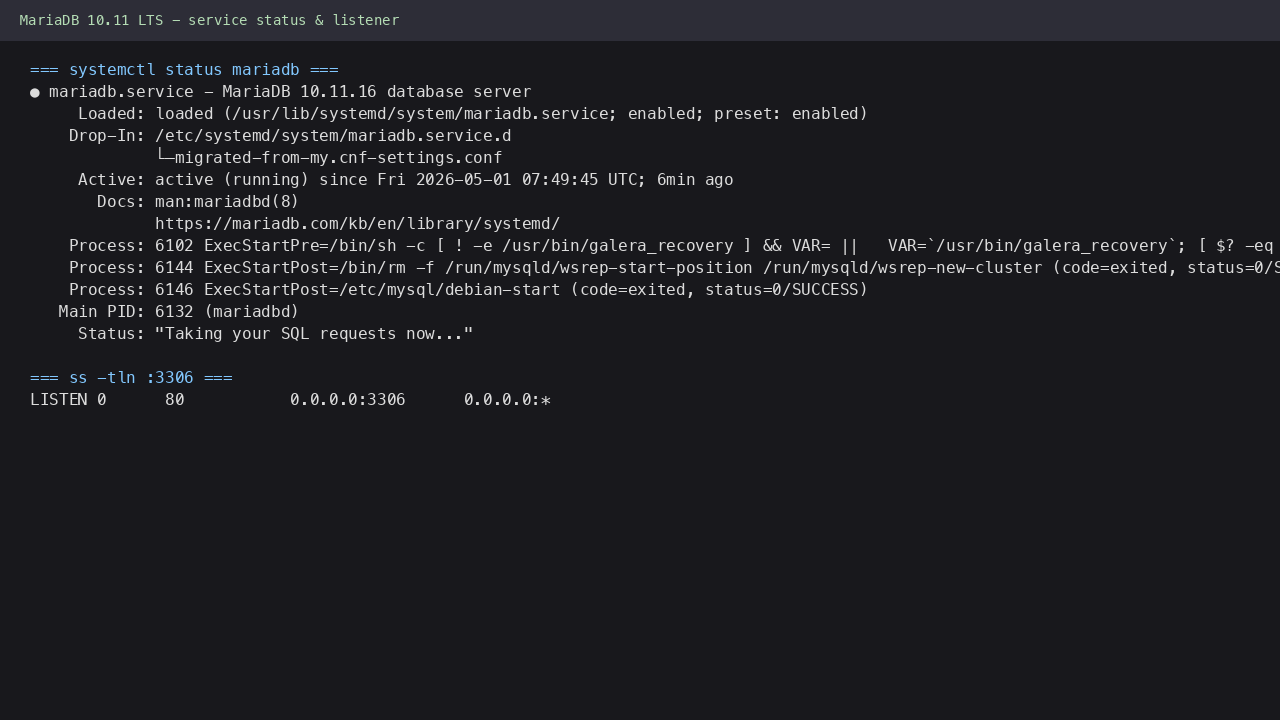
Step 4: Verify the MariaDB Service
sudo systemctl status mariadb.service --no-pager
Expected: active (running). Confirm the firstboot sentinel:
sudo test -f /var/lib/cloudimg/mariadb-firstboot.done && echo FIRSTBOOT_DONE
Confirm the listener:
sudo ss -tln | grep 3306
Step 5: Retrieve Credentials
sudo cat /stage/scripts/mariadb-credentials.log
You will see:
ROOT_USER=root
ROOT_PASSWORD=<ROOT_PASSWORD>
CLOUDIMG_USER=cloudimg
CLOUDIMG_PASSWORD=<CLOUDIMG_PASSWORD>
CLOUDIMG_DATABASE=cloudimg
PORT=3306
Store the passwords in your secret store. The file is mode 0600 (root only).
Step 6: Connect Locally with the mariadb Client
Export the root password to a shell variable for the session:
export ROOT_PW="$(sudo awk -F= '/^ROOT_PASSWORD=/{print $2}' /stage/scripts/mariadb-credentials.log)"
Connect:
mariadb -u root -p"${ROOT_PW}"
You should see the MariaDB prompt:
Welcome to the MariaDB monitor. Commands end with ; or \g.
Your MariaDB connection id is 7
Server version: 10.10.11-MariaDB-ubu2404 ...
MariaDB [(none)]>
Run SELECT VERSION(); to confirm, then \q to exit.
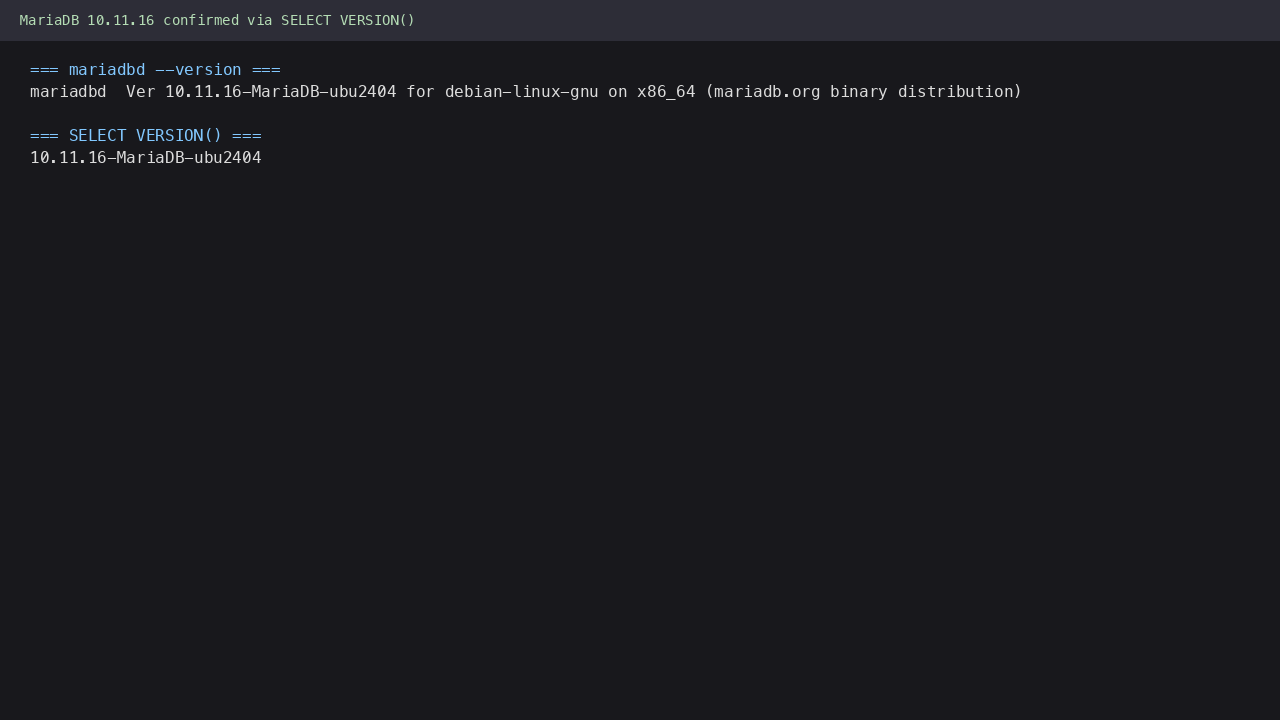
Step 7: Confirm the Version
mariadb -u root -p"${ROOT_PW}" -BNe "SELECT VERSION()"
Expected: 10.10.11-MariaDB-ubu2404 (or similar 10.11).
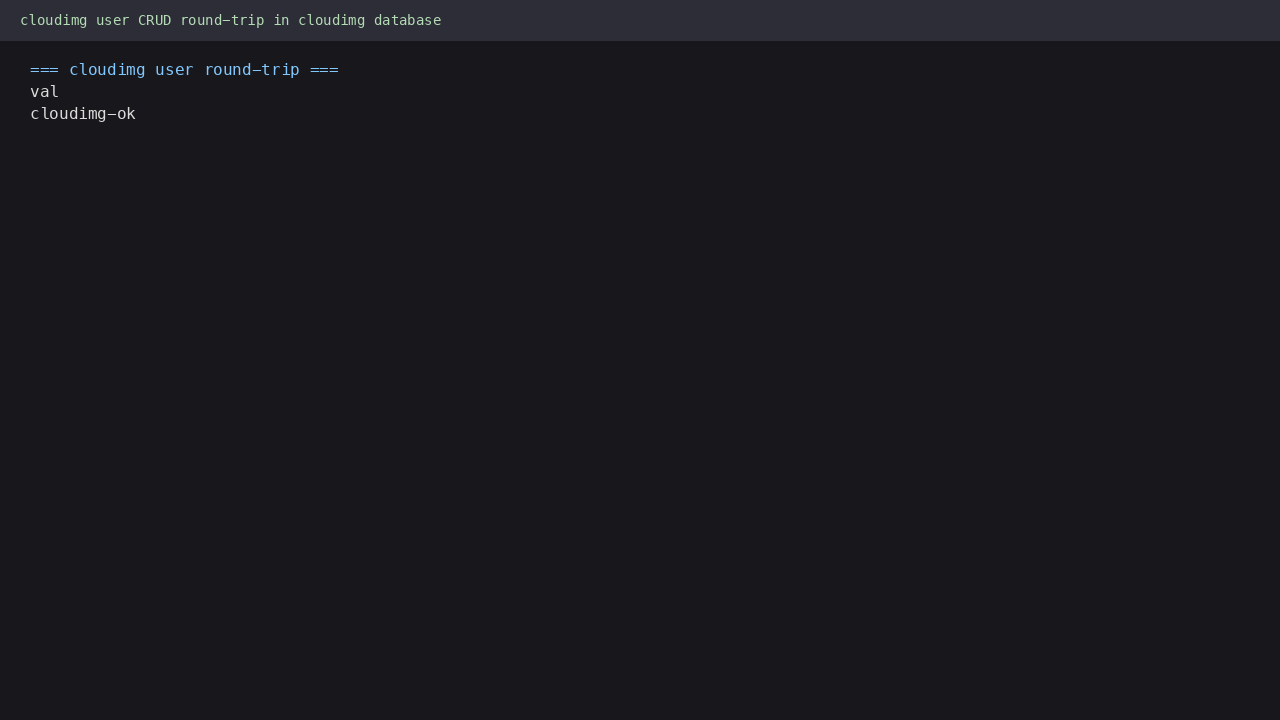
Step 8: Round-trip Test as the cloudimg User
The cloudimg user has all privileges on the cloudimg database:
export CL_PW="$(sudo awk -F= '/^CLOUDIMG_PASSWORD=/{print $2}' /stage/scripts/mariadb-credentials.log)"
mariadb -u cloudimg -p"${CL_PW}" cloudimg -e "
CREATE TABLE IF NOT EXISTS probe (id INT, val VARCHAR(64));
INSERT INTO probe VALUES (1, 'cloudimg-ok');
SELECT val FROM probe WHERE id=1;
DROP TABLE probe;
"
You should see cloudimg-ok.
Step 9: Connect from a Remote Application
The shipped image binds MariaDB to 127.0.0.1 only (Ubuntu noble packaging default — listener on 127.0.0.1:3306, not 0.0.0.0:3306). To accept connections from other hosts in your virtual network, edit /etc/mysql/mariadb.conf.d/50-server.cnf and change the bind-address line:
sudo sed -i 's/^bind-address.*/bind-address = 0.0.0.0/' /etc/mysql/mariadb.conf.d/50-server.cnf
sudo systemctl restart mariadb.service
sudo ss -tln | grep 3306
Confirm the listener is now bound on 0.0.0.0:3306 not 127.0.0.1:3306.
Then from any host inside the same virtual network, on port 3306 with the cloudimg credentials:
mariadb -h <private-ip> -P 3306 -u cloudimg -p'<CLOUDIMG_PASSWORD>' cloudimg
The MariaDB Connector libraries also speak the MySQL wire protocol natively for legacy MySQL clients.
Security note: binding to 0.0.0.0 only matters at the network layer if your NSG actually allows inbound 3306 from somewhere. Keep bind-address=127.0.0.1 if all consumers are on the same VM (the typical LAMP single-server pattern). Use 0.0.0.0 only when you have application servers on different VMs in the same VNet, and pair it with an NSG rule restricting 3306 to those subnets — never to the public internet.
Step 10: Server Components
Component Path
MariaDB server daemon /usr/sbin/mariadbd
mariadb CLI client /usr/bin/mariadb
mariadb-admin /usr/bin/mariadb-admin
mariadb-dump backup /usr/bin/mariadb-dump
Data directory /var/lib/mysql/
Server config /etc/mysql/mariadb.conf.d/
Error log /var/log/mysql/error.log
Systemd unit /lib/systemd/system/mariadb.service
Firstboot script /usr/local/sbin/mariadb-firstboot.sh
Firstboot service /etc/systemd/system/mariadb-firstboot.service
Credentials file /stage/scripts/mariadb-credentials.log
Firstboot sentinel /var/lib/cloudimg/mariadb-firstboot.done
Inspect installed package version:
dpkg-query -W -f='${Package} ${Version}\n' mariadb-server
Step 11: Managing the MariaDB Service
Status:
sudo systemctl status mariadb.service --no-pager
Stop:
sudo systemctl stop mariadb.service
Start:
sudo systemctl start mariadb.service
Restart:
sudo systemctl restart mariadb.service
View error log:
sudo tail -n 50 /var/log/mysql/error.log
Step 12: Tuning for Production
Default config ships with safe defaults that work on small instances. For production VMs, edit /etc/mysql/mariadb.conf.d/50-server.cnf:
-
innodb_buffer_pool_size— set to ~70% of available RAM (default 128M is too small for production) -
max_connections— default 151; raise for high-concurrency workloads -
innodb_log_file_size— default 96M; raise to 512M+ for write-heavy workloads
After editing:
sudo systemctl restart mariadb.service
Step 13: Backups
Use mariadb-dump for logical backups:
sudo mariadb-dump -u root -p"${ROOT_PW}" --all-databases --single-transaction --routines --triggers --events > backup-$(date +%F).sql
For point-in-time recovery, enable binary logging and use mariabackup for hot physical backups.
Step 14: Troubleshooting
Cannot connect on port 3306
-
Confirm service running:
sudo systemctl status mariadb.service -
Confirm listener bound:
sudo ss -tln | grep 3306 -
Check error log:
sudo tail -n 50 /var/log/mysql/error.log -
Confirm NSG allows TCP 3306 from your client source IP
Authentication errors
-
Re-read password:
sudo awk -F= '/^ROOT_PASSWORD=/{print $2}' /stage/scripts/mariadb-credentials.log -
Confirm shell variable not truncated
-
Confirm firstboot completed:
sudo test -f /var/lib/cloudimg/mariadb-firstboot.done && echo OK
Firstboot did not run
-
Check service:
sudo systemctl status mariadb-firstboot.service --no-pager -
Review journal:
sudo journalctl -u mariadb-firstboot.service --no-pager -n 100 -
If MariaDB failed to start, check error log:
sudo tail -n 50 /var/log/mysql/error.log
Service fails to start
-
Check journal:
sudo journalctl -u mariadb.service --no-pager -n 100 -
Check filesystem space:
df -h /var/lib/mysql -
Verify data directory ownership:
sudo ls -la /var/lib/mysql | head; should bemysql:mysql
Step 15: Security Recommendations
-
Rotate the root password on a schedule using
ALTER USER 'root'@'localhost' IDENTIFIED BY '<new-password>'; -
Create application-specific users with minimal privileges; never connect application code as root or as the cloudimg superuser
-
Restrict port 3306 to trusted application server subnets only in your NSG
-
Enable binary logging for replication and point-in-time recovery: add
log_bin = /var/log/mysql/mariadb-binunder[mysqld]in/etc/mysql/mariadb.conf.d/50-server.cnf -
Enable TLS for connections by configuring SSL certificates in
[mariadb]and requiringREQUIRE SSLon user grants -
Back up regularly with
mariadb-dump(logical) ormariabackup(physical) -
Keep MariaDB updated:
sudo apt-get update && sudo apt-get upgrade mariadb-serverperiodically -
Shred the credentials file once the passwords are stored in your secret store:
sudo shred -u /stage/scripts/mariadb-credentials.log
Step 16: Support and Licensing
MariaDB Server is released under the GNU General Public License version 2. There is no per-core, per-seat, or per-server fee for MariaDB Community. MariaDB is a registered trademark of MariaDB Corporation Ab.
cloudimg provides commercial support for this image separately from the upstream project.
-
Email: support@cloudimg.co.uk
-
Website: www.cloudimg.co.uk
-
Support hours: 24/7 with guaranteed 24 hour response SLA
Deploy on Azure
Launch MariaDB 10.11 LTS on Ubuntu 24.04 with 24/7 support from cloudimg.
View on Marketplace
Need Help?
Our support team is available 24/7.
support@cloudimg.co.uk