Memcached 1.6 on Ubuntu 24.04 on Azure User Guide
Overview
This guide covers the deployment and configuration of Memcached 1.6 on Ubuntu 24.04 on Azure using cloudimg Azure Marketplace images. Memcached is the high-performance distributed in-memory key-value cache used by Facebook, Twitter, Netflix, GitHub and Wikipedia to alleviate database load and accelerate dynamic web applications.
The image installs Memcached 1.6 from the Ubuntu 24.04 noble main APT repository (compiled with --enable-sasl). At first boot, memcached-firstboot.service generates a per-VM SASL user (cloudimg) and a 32-character hex password, writes them into /etc/sasl2/memcached-sasldb2 (mode 0640, memcache:memcache), and mirrors them to /stage/scripts/memcached-credentials.log (mode 0600 root only). All client connections must authenticate using the binary protocol with SASL PLAIN. ASCII protocol and anonymous connections are rejected.
The default deployment listens on 127.0.0.1:11211 only. Customers reconfigure -l and -p in /etc/memcached.conf for non-loopback access. Memcached is volatile by design — data lives in RAM only and is lost on restart, so size the cache via -m to fit your working set and use Memcached as a cache, never a primary store.
What is included:
-
Memcached 1.6.x (latest 1.6 at build time, 1.6.24) from the Ubuntu 24.04 noble main APT repository, compiled with
--enable-sasl -
memcached.servicesystemd unit auto-starting on boot -
memcached-firstboot.servicesystemd oneshot that generates the per-VM SASL user and password and writes/etc/sasl2/memcached-sasldb2+/stage/scripts/memcached-credentials.log -
libmemcached-toolspackage formemcstat,memcping,memcdump,memcrm,memcslap,memcexistetc. -
python3-pylibmcpackage preinstalled — SASL-aware Python client over libmemcached -
Default listener on TCP 11211 bound to
127.0.0.1(loopback only) -
Default cache size 64 MB, max connections 1024 (tunable via
-mand-cin/etc/memcached.conf) -
Per-VM SASL credentials enforced — anonymous and ASCII-protocol connections rejected
-
Ubuntu 24.04 LTS base with latest security patches applied at build time
-
Azure Linux Agent for seamless cloud integration and SSH key injection
-
24/7 cloudimg support with guaranteed 24 hour response SLA
Prerequisites
-
An active Azure subscription
-
A subscription to the Memcached 1.6 on Ubuntu 24.04 listing on Azure Marketplace
-
An SSH public key for VM authentication
-
A virtual network and subnet in the target region
Recommended virtual machine size: Standard_B2s (2 vCPU, 4 GB RAM) for development and small caches. Production deployments should use Standard_E4s_v5 (4 vCPU, 32 GB RAM) for caches up to ~28 GB usable, or Standard_E16s_v5 (16 vCPU, 128 GB RAM) for larger caches and session stores. Memcached is memory-bound, so the most important sizing dimension is RAM, not cores.
Step 1: Deploy from the Azure Portal
Navigate to Marketplace in the Azure Portal, search for Memcached 1.6, select the cloudimg publisher entry, and click Create.
On the Networking tab attach a network security group that allows inbound TCP 22 from your management IP range and TCP 11211 from your application VMs. Do not expose port 11211 to the public internet — even with SASL enabled, brute-force attacks against weak passwords are a real risk, and Memcached without TLS leaks both the password and the cached data in cleartext on the wire.
Click Review + create, wait for validation, then Create. Deployment takes around two minutes.
Step 2: Deploy from the Azure CLI
RG="memcached-prod"
LOCATION="eastus"
VM_NAME="memcached-01"
ADMIN_USER="azureuser"
GALLERY_IMAGE_ID="/subscriptions/<sub-id>/resourceGroups/azure-cloudimg/providers/Microsoft.Compute/galleries/cloudimgGallery/images/memcached-1-6-ubuntu-24-04/versions/<version>"
SSH_KEY="$(cat ~/.ssh/id_rsa.pub)"
az group create --name "$RG" --location "$LOCATION"
az network vnet create --resource-group "$RG" --name memcached-vnet \
--address-prefix 10.97.0.0/16 --subnet-name memcached-subnet --subnet-prefix 10.97.1.0/24
az network nsg create --resource-group "$RG" --name memcached-nsg
az network nsg rule create --resource-group "$RG" --nsg-name memcached-nsg \
--name allow-ssh --priority 100 \
--source-address-prefixes "<your-mgmt-cidr>" \
--destination-port-ranges 22 --access Allow --protocol Tcp
az network nsg rule create --resource-group "$RG" --nsg-name memcached-nsg \
--name allow-memcached --priority 110 \
--source-address-prefixes 10.97.0.0/16 \
--destination-port-ranges 11211 --access Allow --protocol Tcp
az vm create \
--resource-group "$RG" --name "$VM_NAME" \
--image "$GALLERY_IMAGE_ID" \
--size Standard_B2s --storage-sku StandardSSD_LRS \
--admin-username "$ADMIN_USER" --ssh-key-values "$SSH_KEY" \
--vnet-name memcached-vnet --subnet memcached-subnet --nsg memcached-nsg \
--public-ip-sku Standard
Step 3: Connect via SSH
ssh azureuser@<vm-ip>
memcached.service will already be running and memcached-firstboot.service will already have generated the SASL credentials.
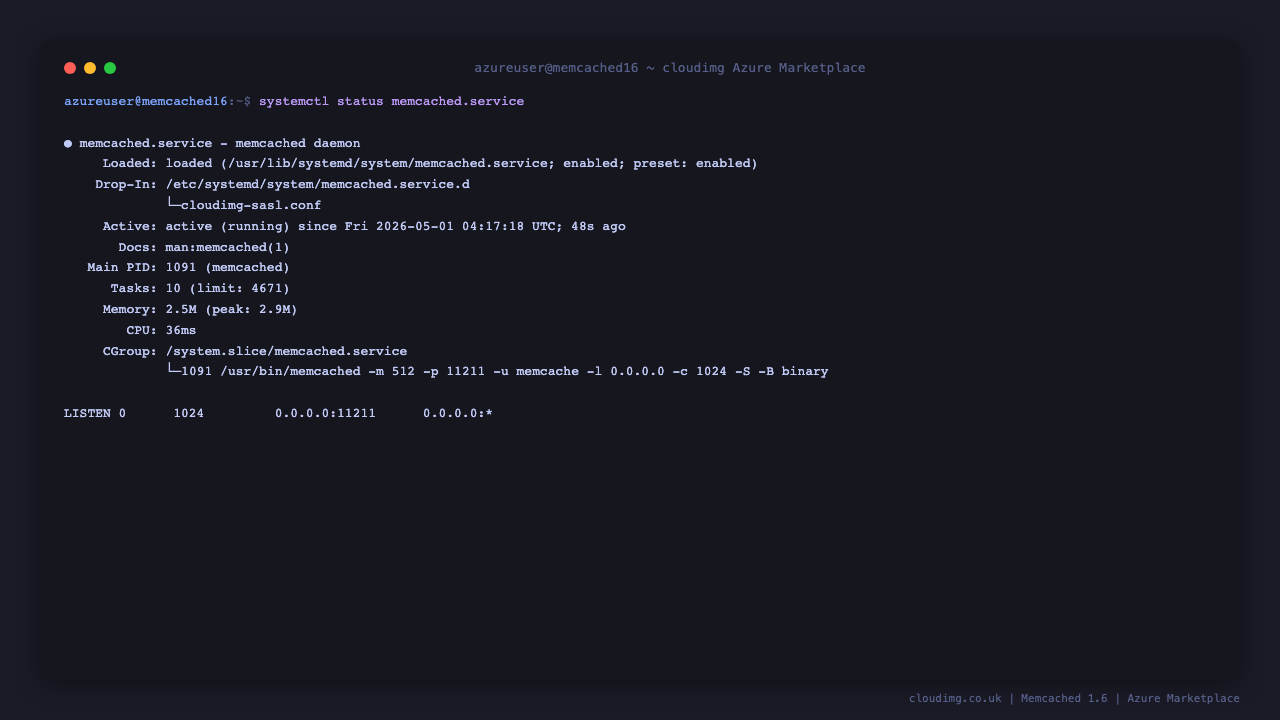
Step 4: Verify the Memcached Service
sudo systemctl status memcached.service --no-pager
Expected: active (running). Confirm the firstboot sentinel:
sudo test -f /var/lib/cloudimg/memcached-firstboot.done && echo FIRSTBOOT_DONE
Confirm the listener is bound on port 11211:
sudo ss -tln | grep 11211
By default Memcached binds to 127.0.0.1 only — LISTEN 0 1024 127.0.0.1:11211. To allow remote connections, edit /etc/memcached.conf and change -l 127.0.0.1 to -l 0.0.0.0 (or your VM's private IP), then sudo systemctl restart memcached.
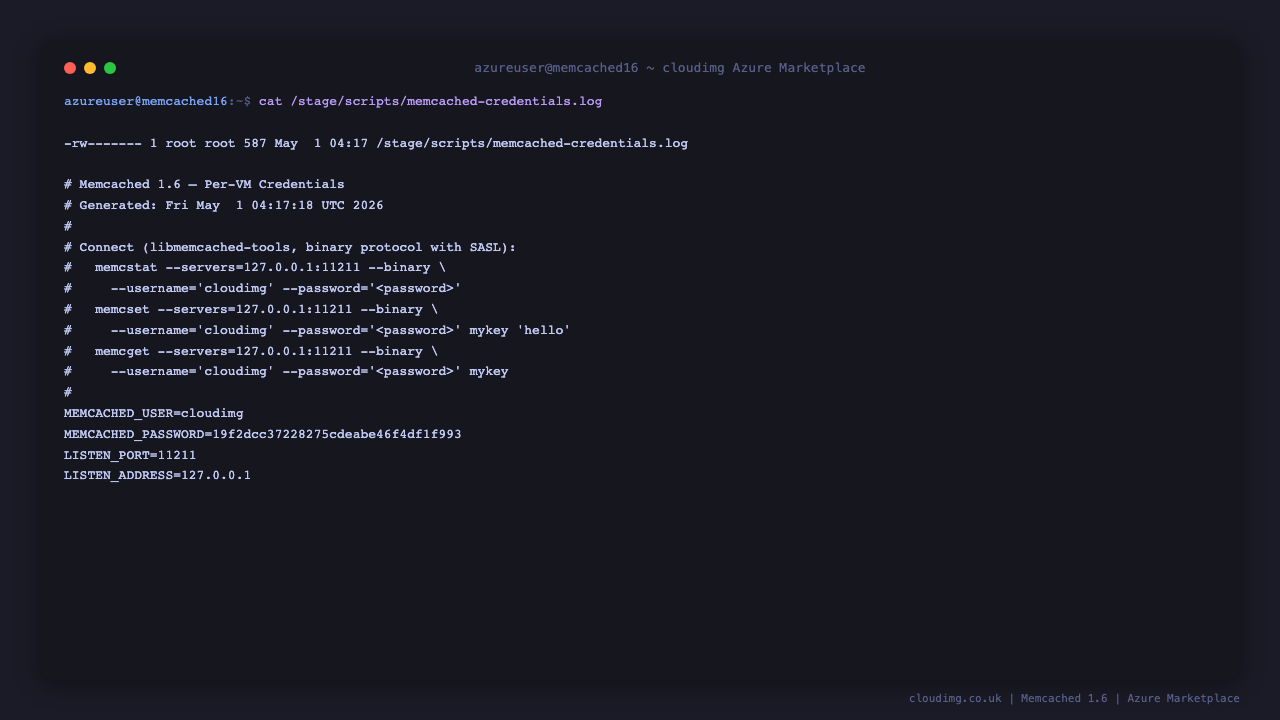
Step 5: Retrieve the SASL Credentials
The SASL user and password have been generated for this specific virtual machine and written to a root-only file. Read them with:
sudo cat /stage/scripts/memcached-credentials.log
You will see lines similar to:
MEMCACHED_USER=cloudimg
MEMCACHED_PASSWORD=<MEMCACHED_PASSWORD>
LISTEN_PORT=11211
LISTEN_ADDRESS=127.0.0.1
Store the password in your secret store. The procedure for rotating the password to a new value is documented in Step 12 below.
Step 6: Connect with libmemcached-tools
The image ships with libmemcached-tools for command-line interaction. Verify the server is reachable and authentication works by reading the rotated password and asking the server for its stats:
PASS=$(sudo grep '^MEMCACHED_PASSWORD=' /stage/scripts/memcached-credentials.log | cut -d= -f2-)
memcstat --binary --username=cloudimg --password="${PASS}" --servers=127.0.0.1:11211 | head -12
Look for Server: 127.0.0.1 (11211) and version: 1.6.24 (or later 1.6.x).
Confirm a wrong password is rejected:
memcstat --binary --username=cloudimg --password=wrong --servers=127.0.0.1:11211 2>&1 | grep -qi 'authentication failure' && echo "AUTH REJECTED"
Expected: AUTH REJECTED.
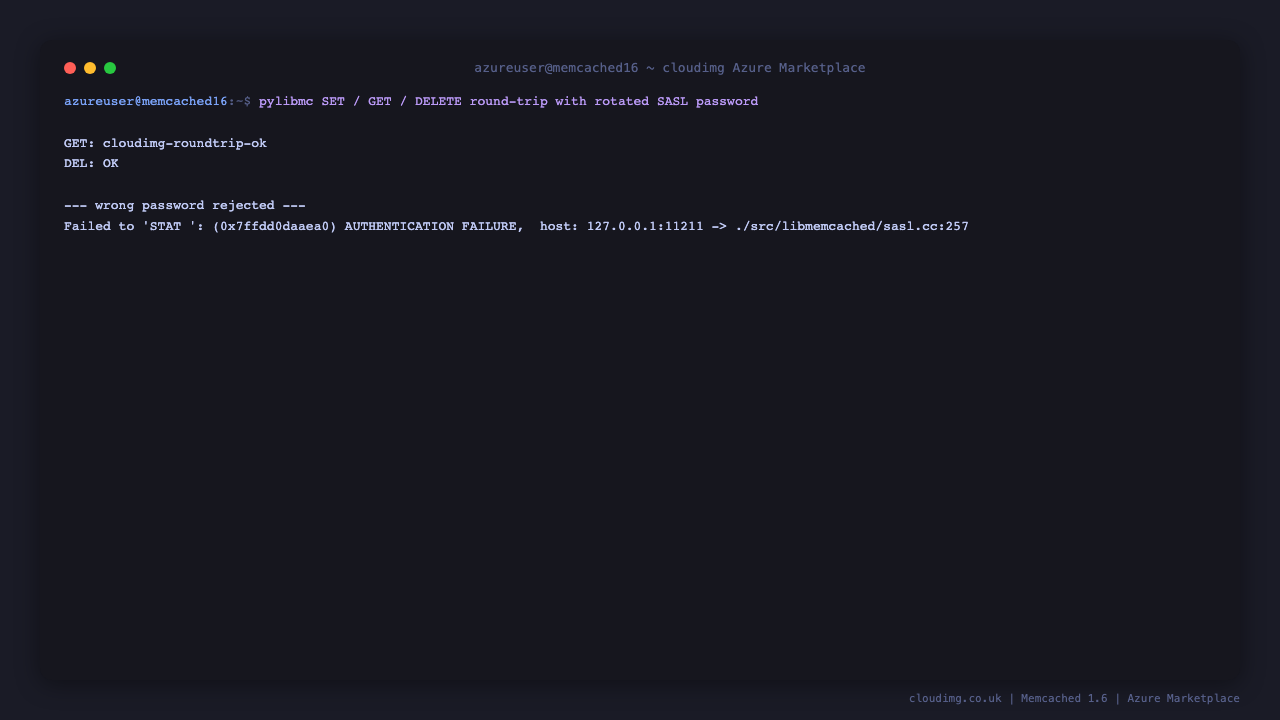
Step 7: Round-trip Test with python3-pylibmc
The image ships with python3-pylibmc, a SASL-aware Python client backed by libmemcached. SET / GET / DELETE a sample key:
PASS=$(sudo grep '^MEMCACHED_PASSWORD=' /stage/scripts/memcached-credentials.log | cut -d= -f2-)
python3 - "${PASS}" <<'PY'
import sys, pylibmc
password = sys.argv[1]
client = pylibmc.Client(["127.0.0.1:11211"], binary=True, username="cloudimg", password=password)
client.set("cloudimg:probe", "cloudimg-ok")
print("get:", client.get("cloudimg:probe"))
client.delete("cloudimg:probe")
print("done")
PY
Expected: get: cloudimg-ok then done.
Step 8: Connect from a Remote Application
From any host inside the same virtual network, install a SASL-capable Memcached client and connect on port 11211 with the rotated credentials.
Python (apt-get install python3-pylibmc or pip install pylibmc):
import pylibmc
client = pylibmc.Client(
["<vm-private-ip>:11211"],
binary=True,
username="cloudimg",
password="<MEMCACHED_PASSWORD>",
)
client.set("hello", "world")
print(client.get("hello"))
Python with bmemcached (pip install python-binary-memcached):
import bmemcached
client = bmemcached.Client(
("<vm-private-ip>:11211",),
username="cloudimg",
password="<MEMCACHED_PASSWORD>",
)
client.set("hello", "world")
print(client.get("hello"))
PHP (apt-get install php-memcached):
<?php
$mc = new Memcached();
$mc->setOption(Memcached::OPT_BINARY_PROTOCOL, true);
$mc->setSaslAuthData("cloudimg", "<MEMCACHED_PASSWORD>");
$mc->addServer("<vm-private-ip>", 11211);
$mc->set("hello", "world");
echo $mc->get("hello");
Ruby (gem install dalli):
require 'dalli'
client = Dalli::Client.new(
'<vm-private-ip>:11211',
username: 'cloudimg',
password: '<MEMCACHED_PASSWORD>',
serializer: JSON,
)
client.set('hello', 'world')
puts client.get('hello')
Do not open port 11211 to the public internet without TLS termination. Memcached cleartext protocol leaks both the SASL password (PLAIN mech) and the cached data on the wire. For production cross-region traffic, terminate TLS at a reverse proxy or compile memcached with -Z and a cert key pair (Memcached >= 1.5.13 supports built-in TLS).
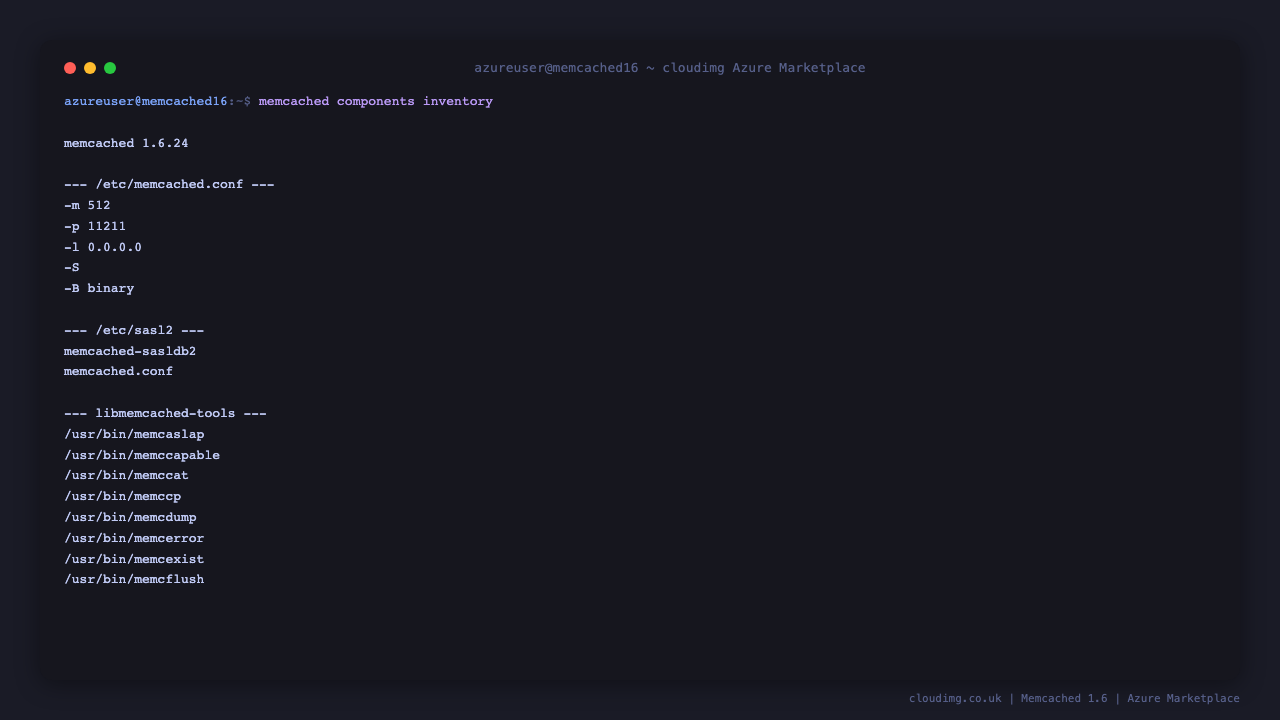
Step 9: Server Components
| Component | Path |
|---|---|
| Memcached binary | /usr/bin/memcached |
memcstat |
/usr/bin/memcstat |
memcping |
/usr/bin/memcping |
memcdump |
/usr/bin/memcdump |
| Main config | /etc/memcached.conf |
| Systemd unit | /usr/lib/systemd/system/memcached.service |
| Systemd drop-in | /etc/systemd/system/memcached.service.d/cloudimg-sasl.conf |
| SASL config | /etc/sasl2/memcached.conf |
| SASL credential database | /etc/sasl2/memcached-sasldb2 (mode 0640 memcache:memcache) |
| Firstboot script | /usr/local/sbin/memcached-firstboot.sh |
| Firstboot service | /etc/systemd/system/memcached-firstboot.service |
| Credentials file | /stage/scripts/memcached-credentials.log (mode 0600) |
| Firstboot sentinel | /var/lib/cloudimg/memcached-firstboot.done |
| Log file | /var/log/memcached.log |
| Python SASL client | /usr/lib/python3/dist-packages/pylibmc |
Inspect the running version:
/usr/bin/memcached --version
Step 10: Managing the Memcached Service
Status:
sudo systemctl status memcached.service --no-pager
Stop / Start / Restart:
sudo systemctl stop memcached.service
sudo systemctl start memcached.service
sudo systemctl restart memcached.service
View the log (Ubuntu's memcached daemon writes to the journal):
sudo journalctl -u memcached -n 50 --no-pager
Resize the cache (memcached must restart to apply):
sudo sed -i 's/^-m .*/-m 512/' /etc/memcached.conf
sudo systemctl restart memcached
Open up to a private IP (after editing your NSG to scope source CIDRs):
sudo sed -i 's/^-l 127.0.0.1$/-l 0.0.0.0/' /etc/memcached.conf
sudo systemctl restart memcached
Drop the entire cache (every key gone):
PASS=$(sudo grep '^MEMCACHED_PASSWORD=' /stage/scripts/memcached-credentials.log | cut -d= -f2-)
memcflush --binary --username=cloudimg --password="${PASS}" --servers=127.0.0.1:11211
Step 11: Troubleshooting
SASL_AUTHENTICATION_FAILED from a client
-
Confirm the password is current:
sudo cat /stage/scripts/memcached-credentials.log -
Confirm SASL is enabled:
grep '^-S' /etc/memcached.conf -
Confirm the sasldb entry exists:
sudo sasldblistusers2 -f /etc/sasl2/memcached-sasldb2
Connection refused on port 11211
-
Service down:
sudo systemctl status memcached -
Listener on different port or address:
sudo ss -tln | grep 11211 -
Firewall blocking: confirm your NSG rules and host firewall
Cache evicting items unexpectedly
-
Memcached's default
-m 64is small. Raise it via-min/etc/memcached.confand restart -
Inspect eviction stats:
memcstat ... | grep -E "evictions|curr_items|bytes"
Cleartext protocol / non-binary client cannot connect
-
The image enforces binary protocol via
-B binaryin/etc/memcached.conf. SASL only works on the binary protocol. ASCII protocol is rejected by design. -
Configure your client library with the binary protocol option (
binary=Truein pylibmc,OPT_BINARY_PROTOCOLin PHP Memcached, etc.)
Step 12: Rotating the SASL Password
To rotate the SASL password to a new value, regenerate the sasldb entry and update the credentials file:
NEW_PASS=$(openssl rand -hex 16)
echo -n "${NEW_PASS}" | sudo saslpasswd2 -p -a memcached -f /etc/sasl2/memcached-sasldb2 cloudimg
sudo chown memcache:memcache /etc/sasl2/memcached-sasldb2
sudo chmod 0640 /etc/sasl2/memcached-sasldb2
sudo systemctl restart memcached
sudo sed -i "s/^MEMCACHED_PASSWORD=.*/MEMCACHED_PASSWORD=${NEW_PASS}/" /stage/scripts/memcached-credentials.log
echo "Rotated. New password stored in /stage/scripts/memcached-credentials.log"
After rotating, update any client configurations that hold the old password.
Step 13: Security Recommendations
-
Rotate the SASL password immediately after deployment — see Step 5
-
Restrict NSG so port 11211 is only reachable from your application VMs and admin networks; never expose to the public internet
-
Enable TLS for any cross-VM connection — Memcached cleartext leaks both the SASL password (PLAIN mech) and the cached data
-
Size the cache correctly via
-mso eviction does not hammer your application's database fallback -
Treat Memcached as a cache — it is volatile by design. All keys disappear on restart. Never use it as a primary data store
-
Patch the OS monthly with
sudo apt-get update && sudo apt-get upgrade && sudo reboot -
Monitor
evictions,curr_items,bytes,cmd_get,cmd_setviamemcstat— sudden swings flag application-level cache misses or DDoS -
Add a second Memcached node for warm-failover: clients with consistent hashing (pylibmc, dalli) handle multi-node clusters natively
Step 14: Support and Licensing
Memcached ships under the BSD-3-Clause license — permissive, friendly to commercial use and modification.
cloudimg provides commercial support for this image separately from the upstream project.
-
Email: support@cloudimg.co.uk
-
Website: www.cloudimg.co.uk
-
Support hours: 24/7 with guaranteed 24 hour response SLA
Deploy on Azure
Launch Memcached 1.6 on Ubuntu 24.04 with 24/7 support from cloudimg.
View on Marketplace
Need Help?
Our support team is available 24/7.
support@cloudimg.co.uk